
Clients of a long-running email marketing platform are getting targeted with a phishing campaign telling them that their emails would begin automatically inserting a “‘Support ICE’ donation button” into every email they send. The strategy suggests that scammers are trying to capitalize on people’s revulsion to ICE by coming up with strategies that would cause users to quickly log into their accounts to disable the setting. In reality, clients would be revealing their username and password to hackers.
The move indicates that hackers are targeting clients of enterprise software companies with extremely controversial political emails. The scam targeted customers of Emma, a long-running email marketing platform whose clients include Orange Theory, Yale University, Texas A&M University, the Cystic Fibrosis Foundation, Dogfish Head Brewery, and the YMCA, among others. 404 Media was forwarded a copy of the phishing email from an Emma client.
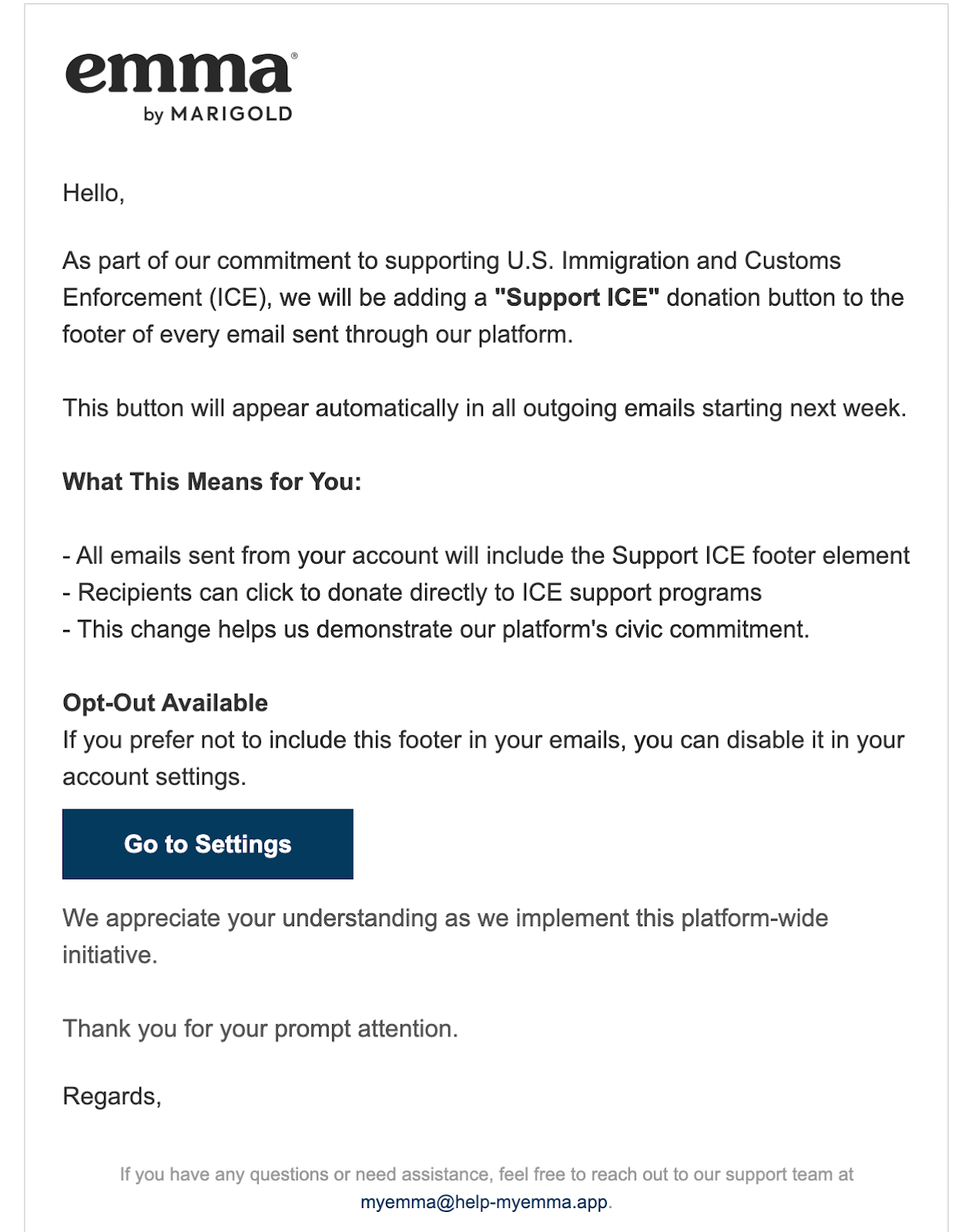
“As part of our commitment to supporting U.S. Immigration and Customs Enforcement (ICE), we will be adding a ‘Support ICE’ donation button to the footer of every email sent through our platform,” the phishing email reads. “This button will appear automatically in all outgoing emails starting next week […] all emails sent from your account will include the Support ICE footer element […] this change helps us demonstrate our platform’s civic commitment.” The email adds that it is possible to opt out of this feature, and that “we appreciate your understanding as we implement this platform-wide initiative.”
Lisa Mayr, the CEO of Marigold, which owns Emma, told 404 Media that the company “would never publish anything like this. This is a very common phishing attempt.”
Mayr is right—clients of other email sending services have recently been targeted with similar attacks. In January, programmer Fred Benenson wrote about phishing emails he had gotten that were targeting users of SendGrid, another email marketing service. At least one of the emails Benenson got used the same “Support ICE button” language and has the subject line “ICE Support Initiative.”
“If you’ve been paying any attention at all to US politics, you’ll know how insidiously provocative this would be if it were a real email,” Benenson wrote in a blog post about the email. “This phishing campaign is a fascinating example of how sophisticated social engineering has become. Instead of Nigerian 419 scams, hackers have evolved to carefully craft messages sent to professionals that are designed to exploit the American political consciousness. The opt-out buttons are the trap.”
In SendGrid’s case, Benenson found that the emails looked “real” because they were sent from other SendGrid user accounts. Basically, hackers compromised the account of a SendGrid user and then used that account to send phishing emails using the SendGrid infrastructure. “The emails look real because, technically, they are real SendGrid emails sent via SendGrid’s platform and via a customer’s reputation–they’re just sent by the wrong people and wrong domains,” he wrote.
Besides the ICE-themed phishing emails, Benenson also received an email that said SendGrid was going to add a “pride-themed footer to all emails” and another that said “all emails sent from your account will feature a commemorative theme honoring George Floyd and the Black Lives Matter movement.”
“The political sophistication on display here (BLM, LGBTQ+ rights, ICE, even the Spanish language switch playing on immigration anxieties) suggests someone with a deep understanding of American cultural fault lines,” Benenson wrote.
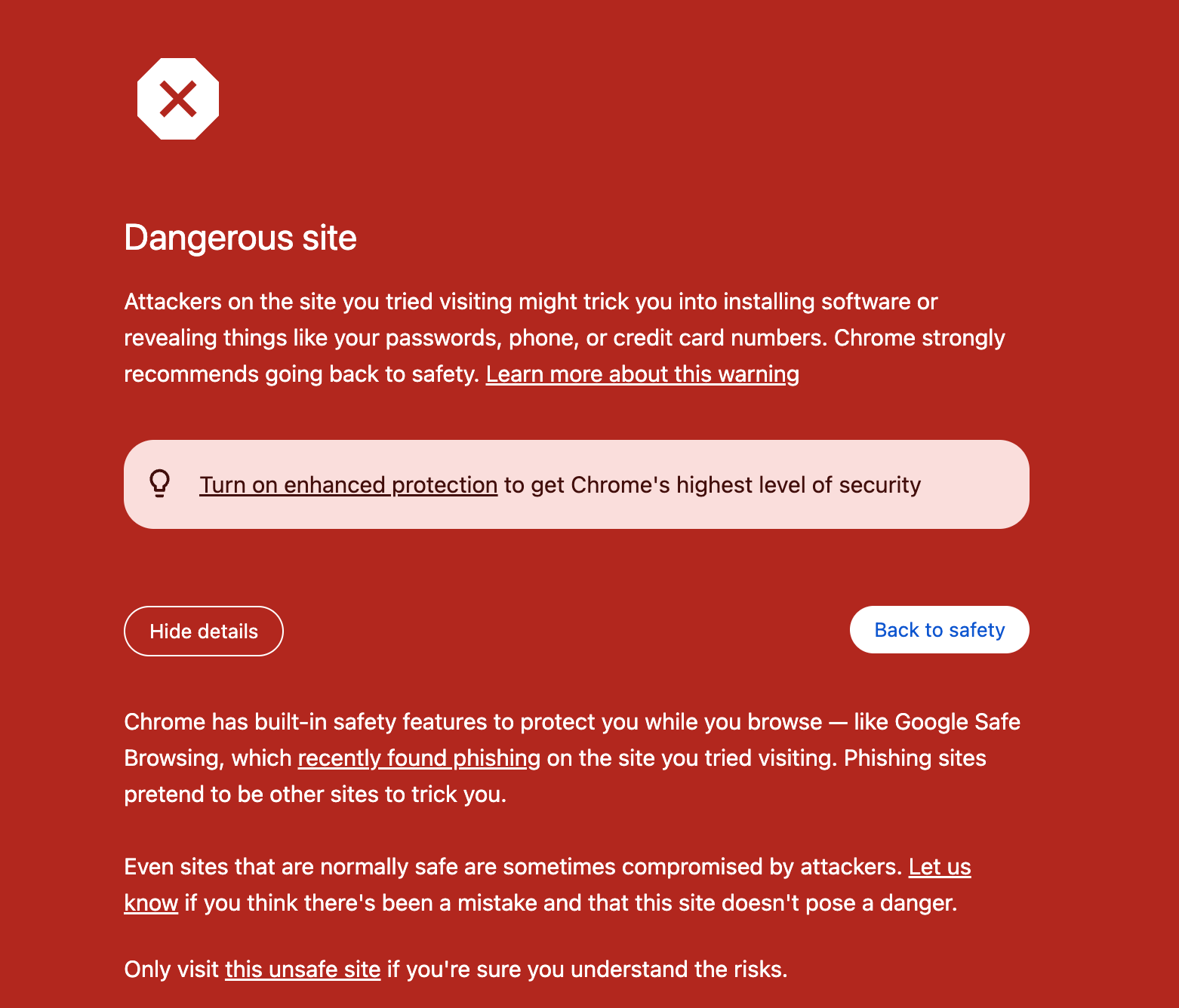
The Emma email was sent via Survey Monkey through an email address called “myemma@help-myemma.app.” When users clicked a “Settings” button that would have allowed them to opt out of the feature, they’re sent to a generic-looking site designed to steal credentials hosted at app-e2maa.net. By the time 404 Media got the email, Chrome had detected it as a “Dangerous site” and warned users not to visit it.
